Key Findings
The proposed measures focus on enhancing transparency, strengthening security controls, improving incident response capabilities, and ensuring stricter regulatory compliance. This research underscores the need for proactive data protection strategies to safeguard personal information and maintain consumer confidence in an increasingly digitised economy.
Recommendations
- Enhancing Transparency: Organisations should implement clear and accessible privacy policies, providing users with granular control over their data.
- Strengthening Security Measures: Adoption of zero-trust architectures and multifactor authentication should be prioritised to mitigate access-related vulnerabilities.
- Regulatory Enforcement: Increased oversight, including periodic compliance audits and sector-specific guidelines, would facilitate more consistent adherence to data protection regulations.
Conclusion
The analysis highlights key findings related to public perception, organisational transparency, sector-specific vulnerabilities, and regulatory compliance within an evolving cybersecurity environment. An emphasis needs to be placed on enhanced regulatory oversight, proactive cybersecurity strategies, and greater transparency in data handling practices to strengthen consumer trust and organisational resilience against evolving threats.
]]>A recent update from CrowdStrike led to widespread system crashes due to a null pointer dereference in C++ code. This incident underscores the critical importance of proper null pointer handling in system-critical software.
Summary of the Article
The forced update from CrowdStrike resulted in system crashes, traced back to a null pointer dereference in system driver code. This caused memory access violations, leading to the infamous blue screen of death (BSOD) on affected systems.
Key Points:
- Null Pointer Errors in C++: Null pointers represent invalid memory addresses, and dereferencing them can cause system crashes.
- Critical System Drivers: Errors in system drivers, especially those loaded during the boot process, have severe consequences, leading to complete system failures.
- Error Analysis: The crash was caused by an unverified null pointer, attempting to access a memory address (0x9c) without validation.
- Widespread Impact: The incident affected multiple sectors globally, including finance, aviation, healthcare, and media.
The CrowdStrike incident highlights the necessity of rigorous code testing and modern programming practices to prevent such failures.
Download the Full Article
For a detailed analysis of the CrowdStrike incident, including code examples and the impact on various sectors, download the full PDF article below:
Stay informed and ensure robust coding practices to prevent similar issues in your software development projects.
]]>Information warfare and cybersecurity postures are strategic imperatives in modern governance, yet the Trump administration’s approach to information security has been largely reactive and inconsistent. This article critically examines the administration’s policy, including its failure to prioritise cybersecurity in national defence strategy, the dismantling of expert oversight mechanisms, and the rollback of essential regulations that safeguard critical infrastructure.
Summary of the Article
The Trump administration’s cybersecurity strategy appears as an afterthought, despite the United States being subject to repeated cyber intrusions. Key failures include:
Key Points:
- Neglecting cybersecurity in national defence strategy: Cybersecurity threats have been deprioritised, despite their increasing prominence in modern conflict.
- Dismantling expert oversight mechanisms: The administration terminated all advisory committees of the Department of Homeland Security (DHS), including the Cyber Safety Review Board (CSRB), weakening regulatory accountability.
- Regulatory rollbacks: Repealing stringent cybersecurity requirements has increased systemic risks across critical infrastructure.
- Emphasis on offensive cyber operations over defensive resilience: A focus on offensive capabilities without corresponding defensive investments weakens national security.
- Abandonment of counter-disinformation initiatives: The removal of key disinformation countermeasures has left the digital battlefield open to manipulation by foreign adversaries.
The administration’s approach has undermined national security, weakened resilience against state-sponsored cyber threats, and left the private sector vulnerable to systemic risks. A structured, evidence-based cybersecurity policy—rooted in regulatory consistency, expert oversight, and proactive defence—is essential to ensuring the security and stability of national infrastructure.
Download the Full Article
For a detailed analysis of the Trump administration’s cybersecurity policies, including historical examples and contemporary cybersecurity frameworks, download the full PDF article below:
Stay informed and ensure robust cybersecurity practices to prevent strategic vulnerabilities in governance and policy.
Share this Article
]]>Introduction
Recent updates in Windows 11 have significantly altered Microsoft’s approach to user privacy. The new Microsoft Outlook, integrated into the latest Windows 11 update, and the introduction of Copilot+ Recall have raised substantial privacy concerns.
Summary of the Article
The updated Microsoft Outlook for Windows, by default, syncs user data, including credentials and emails, to Microsoft Cloud, even for third-party accounts like Gmail, unless users opt out. This practice highlights significant privacy issues and the extensive data collection facilitated by this feature. Additionally, the Copilot+ Recall feature, which continuously takes “screenshots” of the user’s PC to create a searchable database, further exacerbates privacy concerns.
Key Points:
- Extensive Data Collection: Outlook gathers a wide range of user data, including emails, contacts, events, geolocation data, and browsing history.
- Opt-out, Not Opt-in: Users must manually opt out of data sharing, making privacy protection difficult.
- Lack of Transparency: Microsoft’s privacy policy is complex, with unclear data usage practices.
- Recall Feature: Continuously takes screenshots of the user’s PC, raising alarms about user privacy and data security.
The reaction to these changes has been overwhelmingly negative, with significant concerns from cybersecurity communities and privacy advocates.
Download the Full Article
For a detailed analysis of these privacy issues and the potential implications for users, download the full PDF article below:
Stay informed and protect your privacy by understanding the latest changes in Microsoft’s privacy policies and their impact on your personal data.
]]>The Saga continues…
It’s a Friday night, and here I am dissecting a new Spear phishing attack. However, this one has taken my breath away, since the social engineering aspects of this attack have been exceptionally well done, which makes it very dangerous. And whilst this you may have seen before, it was targetting older people as it was attacking Care Homes.
The email is genuine, and replying to a thread you have already communicated with
It’s a genuine email, it passes SPF, DKIM and DMARC checks, does come from someone that you know, and originates from an Outlook client. They are also replying to a thread you have already communicated with.
The link is also interesting. Normally users check the links in their email, and they do this by us either educating them to hover the mouse over the URL, or by using MIMECAST or another similar tool. Well, if they do - it is a genuine OneDrive link, it is just a personal OneDrive or OneNote page share with no user authentication instead. You then click that link which redirects you to the login screen that is a carbon copy of the Office 365 login, with a Let’s Encrypt certificate and a new URL - where your user has become relaxed and the security tools you have in place (Email scanning, URL scanners) are no longer providing any input.
So the URL is different and not Office 365/Microsoft OneDrive?
Yes, it is. But only on the second click from the users’ perspective. The first one is a genuine OneDrive link in their email from a genuine email with someone you have corresponded too, which looks the same as an Office 365 link. So, from the user’s perspective - they’ve checked the originator, and the email is genuine. They’ve checked the URL, and it is genuine. If you use MIMECAST or a similar service, it passes the checks. They then open the email and they have checked the URL at the top of their browser. They confirm it’s an Office link. They then are embarking on their usual user flow - which is when the user is taken out of the Microsoft ecosystem, as the URL in the OneNote page is to an external service, as it is a carbon copy of the Office 365 login page. If you fill in the details, you are then redirected to another page that has a valid SSL certificate. Which contains the Emotet virus. As Emotet spreads by infecting mailboxes, the vicious cycle continues [1].
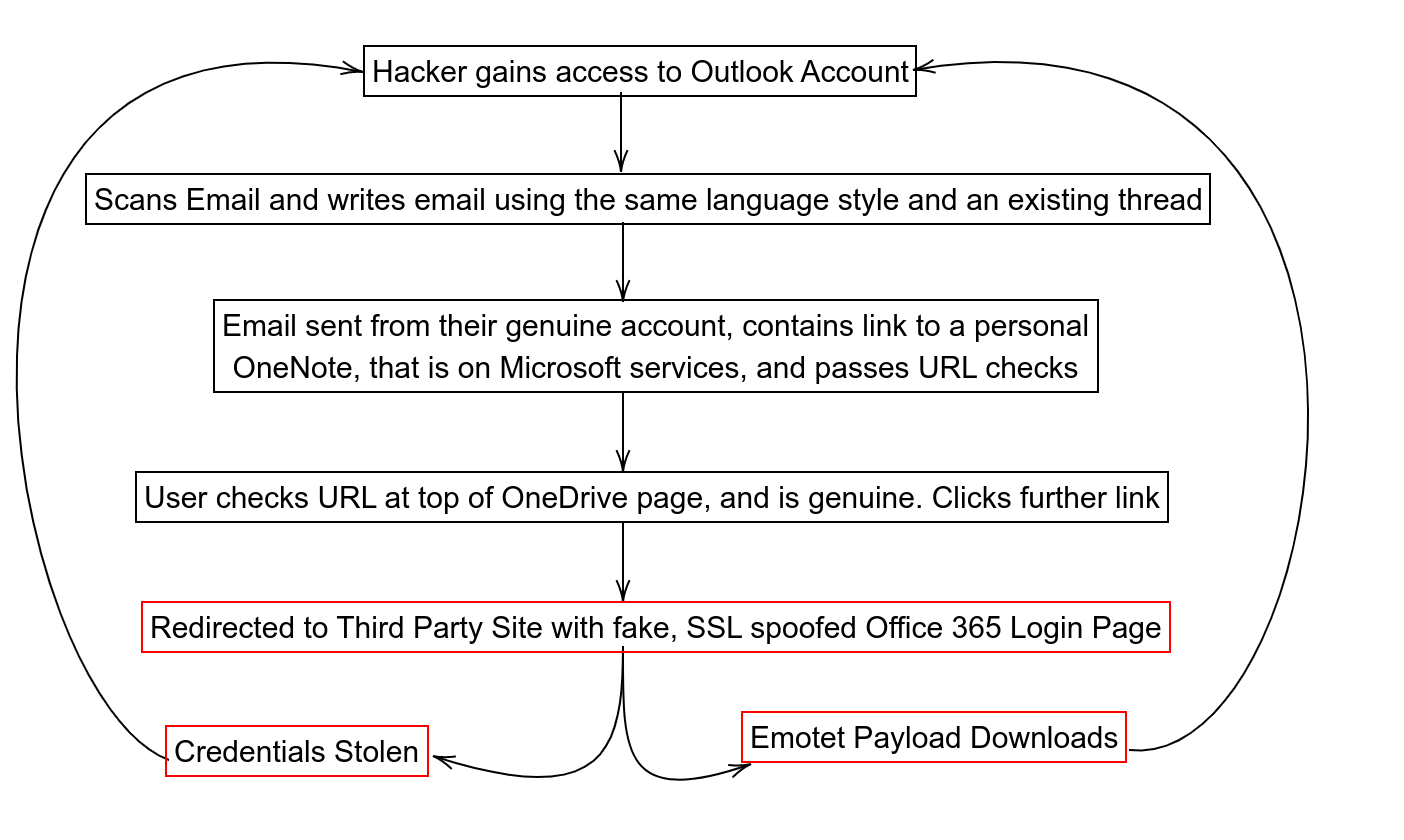
Figure 1.1: User flow of the OneDrive Social Engineering Attack
Each process from this point, however, they have seen SSL certificate green ticks so there are no warning signs for the user, and you have relaxed the user in case they had any worries. If you followed your cybersecurity advice, you most likely would have complied with all of their advice until you got to the exploit, and by then you are already in your safe space.
It also makes abuse reporting procedures harder, as there are multiple places you need to report the violation.
Advice
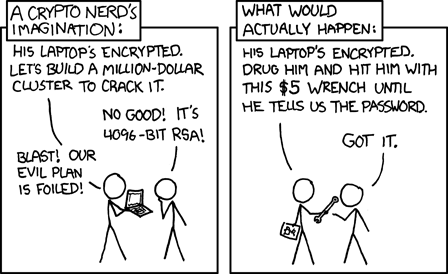
Remember, in your cybersecurity training, do cover the difference between Phishing and Whaling and Spear Phishing. If you are targeted, and they want you - they will get access. Someone will fall for it. You need to make sure the user can identify when it went wrong, and report it to your security team as soon as possible.
Speed is what is important. The quicker you act, the quicker it stays an event rather than an incident.
Most cybersecurity training only covers things like “email addresses that look like someone you know” or “someone you don’t know”. They can be from someone you DO know, and a genuine email. The URL might be have SSL and be genuine. Until it isn’t.
Remember, as we provide mitigations, they adapt. And never, ever blame the users, because sometimes - it’s your procedures and advice that made them trust the email.
References
[1] What is Emotet
]]>The Saga continues…
Back all those years ago, when Britain decided to vote for Brexit, the Brexiters could not have been more delighted. They got their precious Brexit, which for those that know me, I was never for. The same reason I was pro the Union for the United Kingdom to stay with our Scottish friends, is the same reason I thought we were better in Europe. Better together, weaker apart.
However, Brexit happened. Democracy had spoken. And unfortunately, it is now not speaking anymore, it is screaming “it is not working”.
Liz Truss will just be the latest one to go (it will be hours and days, not weeks [EDIT: Okay, it was literally one hour until she resigned]). Johnson, May, Cameron - all have been purged by Brexit.
So, what happened?
The problem happened because it’s the campaign’s very design, and why Brexit was the root cause of these issues, but it is not got anything to do with the European Union. It’s the problem with winning using populist politics, and politics that is completely led by data analytics, and not a clear strategy.
What do you mean?
Brexit won the vote by promising multiple versions of Brexit. All of them are incompatible with each other. The so-called ‘Singapore-upon Thames’ approach on one side, being mass market deregulation across the financial, employment, and other sectors, whilst moving to a low tax, low government approach, and on the other a more left Brexit, which was in some ways championed by Johnson (big infrastructure projects, a stronger military presence, a “Global Britain” initiative). Both of these projects, which are wildly opposing each other, are causing this meltdown. Despite Johnson being a moral vacuum, there is one thing to be said about his leadership style. He was a good ringmaster to keep these ideologically opposed wings of the party together. The problem was when he left, the circus has now no one in charge. The lions are fighting with the clowns.
Brexit Benefits
Like it or not, it has been six years now since Brexit. Jacob Rees Mogg, our Brexit Opportunities Minister, appears to be slightly thin on the ground as he is reporting on our Brexit benefits. We’ve lost frictionless trade, and freedom of movement, but when he was pushed to give us a benefit he stated that ‘we have gained the ability to change the emergency exit signs in the Dartford Tunnel’ [1].
Like it or not, this will be squeaky bum time for the Government. The benefits promised with the sunlit uplands are… not materialising. The pound has been battered. Inflation is skyrocketing. The war in Ukraine continues. You can’t keep promising Jam tomorrow when tomorrow has turned into today.
The Third Way
If growth is Liz Truss’s mantra and wants to increase the country by 5% in growth, the fix is simple but hurtful. Join the European Economic Area.
Like it or not, I don’t think we can rejoin the EU, even though I wish we could. However we can’t be isolated outside of our European friends with these false Brexit promises anymore that have not materialised. To quote Rory Stewart:
I hate the word “appeasement” which is thrown around by both sides in this debate. We live in a society where good people can reasonably disagree - and where compromise is an essential democratic virtue - reflecting our pluralism. We should have compromised on Brexit. https://t.co/ethfwiKCTF
— Rory Stewart (@RoryStewartUK) December 5, 2020
I think within the coming months, we will be forced to decide on our place within Europe. It will be humbling for the UK, but it will be a necessary move to make.
[1] EU gave us ‘very funny numbers’: Rees-Mogg on new post-Brexit laws - LBC
]]>Problem
Another year, another load of articles saying that cyber threats are the worst they have ever been. Yet, still, consistently, the worst thing is the attitude of some cyber practitioners. Day after day, month after month, we see silly comments loaded with attitude from our professional community. This attitude plays a key part in why the cyber risk is getting worse.
``Look at company X, how dare they don’t do security, they are just crap” etc etc.
This attitude is toxic, for several reasons - but it is also incredibly stupid. Why? Well, so far, the most prevalent cybersecurity people on LinkedIn that go after companies publicly have just a proven track record of their ineptitude (along with anyone that goes along with it spreading it without verifying), because 99% of cases are complete false positives. Additionally, so far, since I am that guy - most of the people stating these blindingly obvious vulnerabilities they have detected (their words, not mine) on these companies have got serious critical issues of their own. Therefore they end up cementing the ``do as I say, not as I do” approach to cybersecurity, which isn’t my recommended security posture for any organisation.
Unethical Hacking
However, let’s say for argument’s sake, they do find a vulnerability, it is genuine. And you report it as a personal ego boost or an advert for your cyber company. Let’s break that down.
If I found your wallet in the street, I would find you by using the name on your credit card on social media, and attempt to contact you. If I couldn’t find you, I would then hand the wallet to a local police station, and go about my day.
I would not take a picture of your credit card, front and back, and put it on a website tagging the person saying “this person is a complete moron. Left their wallet in the street. Exposed their own credit card!”
Catch my drift? If you do this, please do add the letters ‘un’ into your job title of Ethical Hacker.
However, my biggest gripe with this attitude is the fact that if that is how you communicate externally about this, it affects how you communicate your cybersecurity risks and issues internally, to your company, to your friends, and this makes a huge problem.
People make mistakes. People have lives. During a time of a crisis, an incident, or a security vulnerability, they need to know that there is a friendly neighbourhood cyberperson available who will help, guide, train, nurture, and assist in a way that betters cybersecurity as a whole.
What they don’t need is someone going immediately to ``Hands of Blaming Stations”. If we had an accident on a ship, like I had when HMS Grimsby decided to become the little ship that could become a Tank in Norway, we decided to deal with the flood and crisis first, rather than work out who was to blame. That focus, the `After Action Report’, if you will, is important, but can happen at another time - and you focus on roles and positions, not names, to stop it from becoming the blame game.
All of this concludes into something we should understand about people. Labelling Theory. If you don’t know it, and you are working in cyber, you should. There are more than enough resources to learn about how your communications can be affected by this, but in a very simple sentence;
“If you treat victims of cybersecurity attacks as idiots, they will comply.”
Victim blaming creates more cybersecurity incidents. Communication breakdowns create more cybersecurity incidents. People not approaching you at the stage when it is a cybersecurity event before it develops into an incident creates more cybersecurity incidents.
And Finally…
On a serious note, we have to better educate ourselves about the fact that things change. I still see companies and organisations recommending three monthly changing passwords, even though we know these reduce your security posture. I still see places using insane password complexity rules that make it impossible for a human to remember, but easy for a computer to crack.
In summary, if you think you are an Expert in everything, you are in the wrong field. Break down these barriers. Become the go to in your organisation. Publicly praise when things go well, quietly educate and lead when things go wrong.
Don’t be “that guy”.
]]>
This is a question I get asked all of the time whenever I go to speak at Conferences, big or small, keynote or ‘session number 57 workgroup B’, which is out by the bike sheds…
And the answer is really simple.
I practice what I preach, so I don’t have anything that could be compromised (I don’t need any), I don’t do any analytics (No Google Analytics, no “Trackers”, no Cookies, nothing).
My webpage is exactly what it is. A static webpage, with no magic, with some content, and my contact details.
Now, you are most likely are thinking I’m about to go on about how everyone else does should follow my lead, but you will be mistaken.
You do you. For most people, this would be too much effort and it would look still look rubbish, and I completely understand that. Businesses can’t make webpages that look like Gopher Sites (for those that don’t know, before the wibbly woberly web, the way you surfed the net was by using ‘gopher’. The link will send you to the Student Run Computing Facilities Gopher service at the University of Cambridge - still up and running!) or something that looks like it belongs to CompuServe or AOL from the 90’s.
However, you should do your best to protect the privacy of your customers to the best of your ability. Only keep what you need.
I know that I would rather be spending my time focusing on my job rather than worrying about if I am going to get a breach on my website that, in the end, just consists of a contacts page, a few pictures, a blog, and some academic articles and news links.
But as a major bonus, it makes my Cookie Policy a really and simple one.
Cookie Policy
If you would like to send Kieren a cookie, please don’t and instead send M&S Jaffa cakes. The lime ones.
Or a box of Pickled Onion Monster Munch.
And never any gluten-free cookies, as they all taste like damp cardboard.
So, there you go. That is why my website is not fancy. And since you read all of this post, you earned it; Go get yourself a real cookie, because there isn’t a web one for you here.
]]>Introduction
Within cybersecurity, we have a mantra; Defend, Detect, Deter, Defeat.
Now defence and detection, these are normally quite well established (but of course, it always needs testing and needs improvement). VPN’s, Intruder Detection and Prevention Systems, Managed Desktop Solutions, Firewalls, Single Sign-On systems… the list is endless.
However, deterrence postures and defeating cyber-attacks are normally the two aspects we don’t implement well. We don’t practice enough, and we don’t even really like looking at it. This post describes the problem with of these two subjects, and why they are so, so important.
And what we can learn from the Royal Naval attitude towards crisis management and C3 (Command, Control and Communications).

Deterrence
So, what do we mean by Deterrence? Let’s be honest, your strategic objective is to make sure your staff, third parties, infrastructure and customer data is harder to exploit, or systems are harder to attack, than the company or organisation next to you. We are trying to stop ‘drive-by’ attacks.
It’s not a nice way to think, but it is a fact. You wouldn’t leave your wallet on display, half coming out of your pocket, whilst walking through a crowded Oxford Street. The same applies to our digital footprints. Finding leaked third party credentials linked to your organisation email addresses and accounts, and personal accounts connected to your staff members, need to be identified, isolated and changed because it gives hackers the first breadcrumb to look further into your network or ecosystem.
We have to reduce these breadcrumbs from the start, so they will go somewhere else. Deterrence, however, does not work against someone determined to get into your system by any means. It’s the same with your infrastructure. You have to match sure the back gate is at least locked.
The difference between a drive-by hack and a targetted attack is ‘motivation’. They will get over that back gate, no matter what, if they are motivated.
Motivation?
Give me a technically qualified hacker anytime over a motivated person that hates you. Insider former employee, disgruntled customer, protester groups, ex-partners, state hackers working for a cause… they will get in. Either through human aspects, through technical vulnerabilities, through process hacking (looking at the way you function as an organisation, and find a way to exploit your processes, to find an entry point), the odds are in their favour.
You have 10,000 employees to protect, they each have three work accounts, and if they get spotted, they don’t care. They will keep trying. This mindset and threat aggressor is one we only have one way to deal with: and this is where your team is vital. Not only the security team, everyone.
Defeat
Does your organisation know who to report security issues to? Who would lead your response to a cyber incident? Has your organisation gained the the trust of the security team in order for people to provactively submit anything out of the ordinary for further investigation? Do you have a good cop in your Good cop/bad cop security routine, or is everyone just a ‘bad cop?’ Is the routine to report incidents as simple as calling 112/999? Are physical security problems copied and reported the same way? Do you talk and liaise with other Computer Emergency Response Teams and other SOC’s, including competitors, and share threat information with them?
If the answer is no to any of the above, then you need to practice your incident handling. Don’t just train people to spot detections, train them to deal with what happens when it all goes wrong. From the operational level to activating the strategic crisis management team. Make sure your policies and processes work.
Can you effectively communicate your organisation aim, top priorities, and task individuals, to manage the incident back into business as usual?
Again, if the answer is no, you are going to have a bad day. The quicker you identify, mitigate and communicate an event, the better chance it will remain an event - and not become an incident on the front page of the Daily Mail. During my time in the Navy, we had an incident response golden rule. If the ship’s firefighter turns up to the scene of a fire within 30 seconds with an extinguisher, then the fire is out. If it is over 30 seconds, the ship is lost.
The same applies to cybersecurity. Lead by example, otherwise, you will become the example not to follow in one of my presentations.

Train as you fight, fight as you train.
]]>Introduction
Estonia is one of the countries at the forefront of technology. The country votes online, allows you to digitally sign documents using your Government issued ID card, taxes are fully online, and even prescriptions are done electronically.
As a mentor at Startup Wise Guys as part of their great Cybersecurity accelerator programme, I’ve had the pleasure of being part of a number of startups helping them make an idea become a reality.
There is one thing however, that is quite remarkable though. Most of the companies that join this journey in Estonia are not actually from Estonia, they come from elsewhere in the world to use Estonia as a springboard.
Now, as I was drinking my Coffee this morning, I got tagged by a great friend on LinkedIn asking why this is the case, but I then immediately realised that this is going to be longer than a LinkedIn post. Hence this post.
The state of Cybersecurity
Of course cybersecurity is a challenge everywhere, but within the Estonian ecosystem, the problems and challenges that some people still take for granted elsewhere are less of a concern here. With two factor being the norm for most services, and authentication and authorisation being done from within existing, free Estonian Government backed services, there is a bit of a warped culture when it becomes to cybersecurity product creation.
Wait, what?
Let me explain. Over the years, I’ve had the pleasure of hearing a lot of cybersecurity pitches that are of an excellent calibre. However, for the most part, a lot of them come under the following second catergory.
Technically sound, socially impossible
A number of the products and ideas are designed and produced for the local Estonian or Baltic market - not Europe and the world, alike. It means the product or idea maybe excellent - but no one else needs it. This, in itself, is harmless for the most part, but it does end up with another interesting byproduct.
Disregarding the human aspects of cybersecurity problems and problems needing solutions elsewhere
I hear this more and more; in both my professional and personal life.
- “No one needs x because everyone has two factor”
- “This is so easy, anyone can do it”
- “Who on earth would fall for a dating scam?”
- “Anyone that falls for a COVID related finance scam is an idiot?”
- “Who on earth uses the same username and password for multiple accounts?” (Answer: most of you)
The people that fall for these types of attack are disregarded by Estonian cyber startups, mainly because the level of education within IT, both within the sector and within the general population, is of a high standard. The problem is, Estonia nor the Estonian marketplace should ever be the marketplace you are aiming for. The pool is too small, unless you intend to only remain a specialist provider as a small company. You need to think big. In addition, some of the security tools and practices that are more mainstream here are just not at an ease of use level that is acceptable for consumers whom are not IT experts.
And in the rest of the world, with the activation of lockdowns, these problems (that require innovative solutions) have skyrocketed. The ability to detect targeted spearphishing emails, facebook message scams, sms’s… the ability to help people communicate, work and play from home remotely in a secure fashion, and to work with their Government remotely by digital authentication, has never been needed so much. The market is booming with new players inventing solutions to these challenges, but the ecosystem here in Estonia, that should be rising at the same rate, just isn’t.
Lots of people are at home, they are scared about their futures, and lots of hackers are also bored. Stuck at home. Finding quick ways to get money.
What does this mean? It means that generally criminal groups have done a better job at market research than some cybersecurity startups.
The high quality of the security infrastructure of Estonia is actually (and only in this context is it a bad thing) getting in the way of actual innovation within the cyber sector for the startup scene from the grass roots level. More products and ideas are being formulated for problems that do not exist on the world stage, and problems that are seriously on the rise that need solutions, from countries do not have the security maturity of Estonia, are being disregarded.
In summary; we are ignoring the market where we need to sell because we know better. This isn’t smart.
So, what do we do about it?
Specialize, but not within IT security
More and more industries are now needing tools and advice that requires cybersecurity assistance. In the UK, the NCSC have just released cybersecurity information for Farmers. I’ve been heavily involved over the last few months (and also getting out the ol’ sea legs and giving them some practice) into the maritime cybersecurity sector.
Covid has happened, and that will have forever change the private and public sectors working practices. Some industries have been dragged, kicking and screaming, into the 21st century at breakneck speed.
These global specialist markets now need assistance. They need help. They don’t have your cyber experience. They might need your magic tool.
K.I.S.S (Keep It Simple Stupid)
Whatever product you make, if it isn’t simple, it isn’t a tool - it’s a challenge. And I think we can all agree we have all had enough of them in the last year and a half.
Know what is happening locally, but aim globally
Don’t stay in your bubble. There are certain things that will sell, and certain things that just won’t.
Let’s take the UK, for example, with the ID card. I completely agree, as an avivd user of the Estonian ID card system, it’s an amazing system and makes my life easier. However, trying to sell that to the UK Government, and its population would be a complete meltdown. We tried the ID card idea back in 2008. Why did it fail? The problem is the only place in the UK that has ever had it implemented previously was the Channel Islands. By the Nazi’s. The project was torpedoed immediately, and polling still suggests this will not happen anytime soon. However, utilising a similar system that is purely digital, that might have merit.
We need to take the ideas and knowledge from Estonia, and tailor for Global markets. We do not need to ‘cut and paste’. It won’t work
Conclusion
We have the expertise. We have the ecosystem. We now need to seriously look at what the market wants, not what we think they need. We also have to stop looking at how our life is in Estonia and we have to stop treating this as the norm. It really, really isn’t. And I’m saying that as I look over my desk, and see a lovely ten page document I have to fax over to the UK on monday morning, as they required a signature…
]]>